Settings
A variety of CFEngine and system properties can be changed in the Settings view.
Opening settings
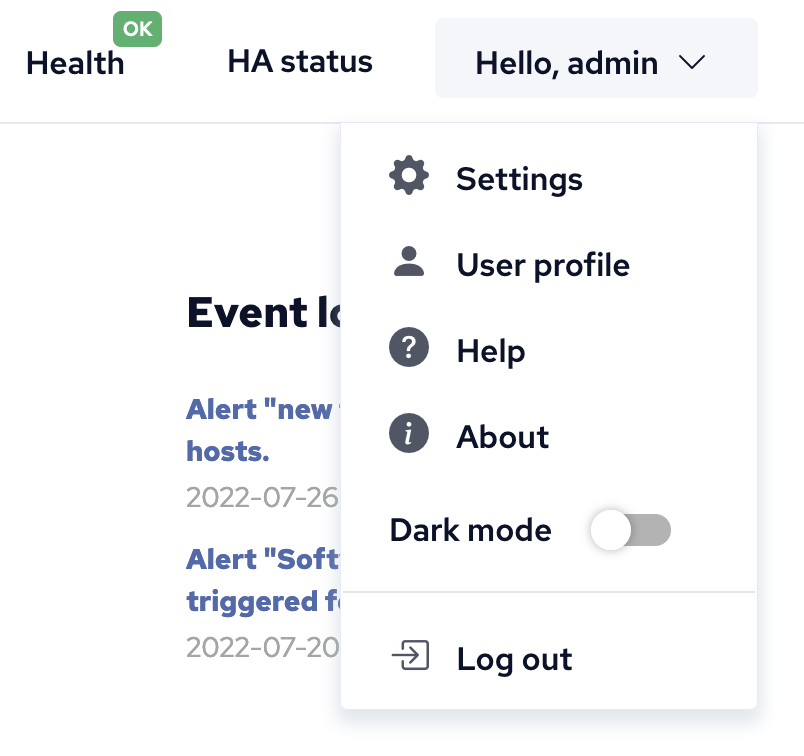
Settings are accessible from any view of the mission portal, from the drop down in the top right hand corner.
Preferences
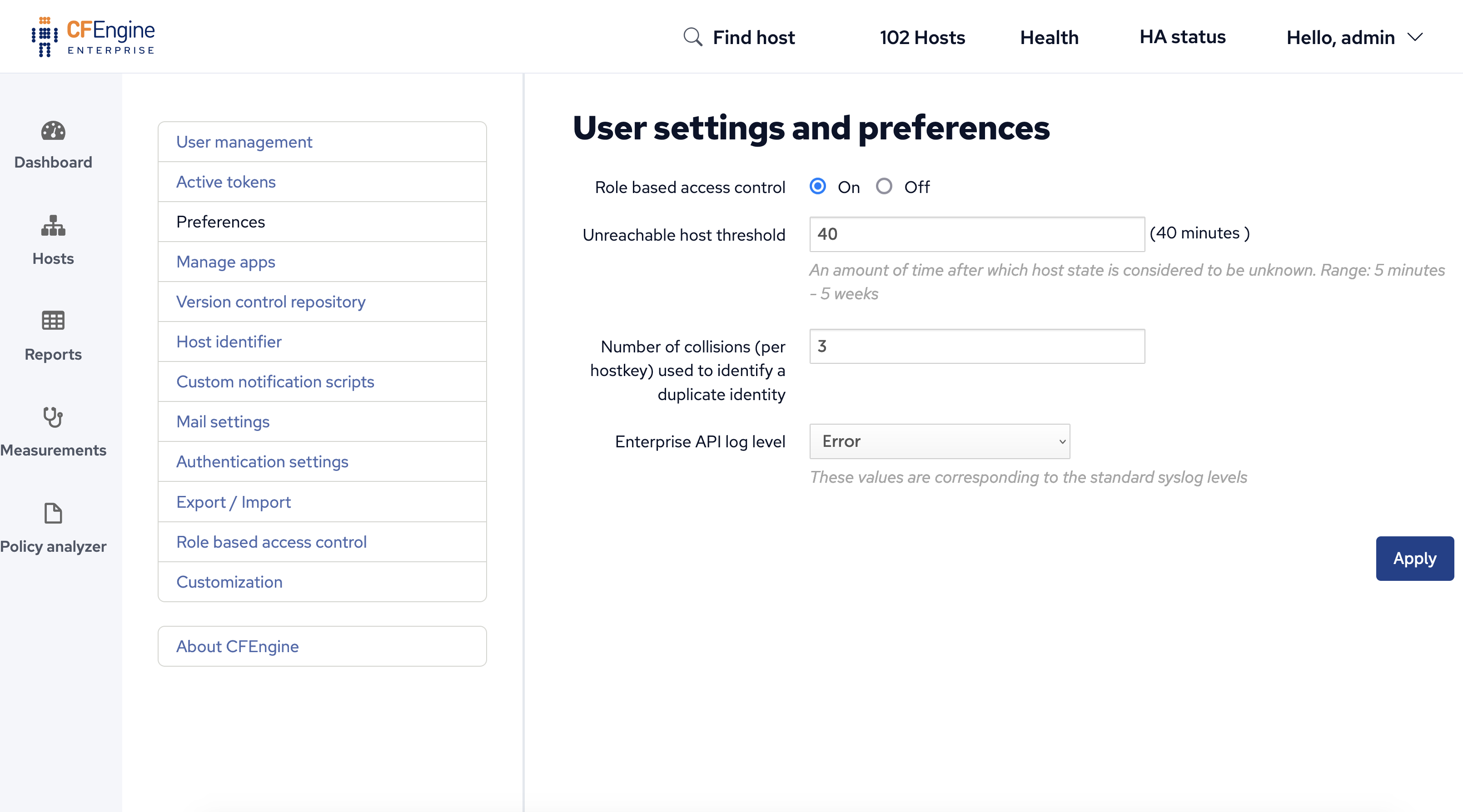
User settings and preferences allows the CFEngine Enterprise administrator to change various options, including:
- Turn on or off RBAC
- When RBAC is disabled any user can see a host that has reported classes
- Note, administrative functions like the ability to delete hosts are not affected by this setting and hosts that have no reported classes are never shown.
- Unreachable host threshold
- Number of samples used to identify a duplicate identity
- Log level
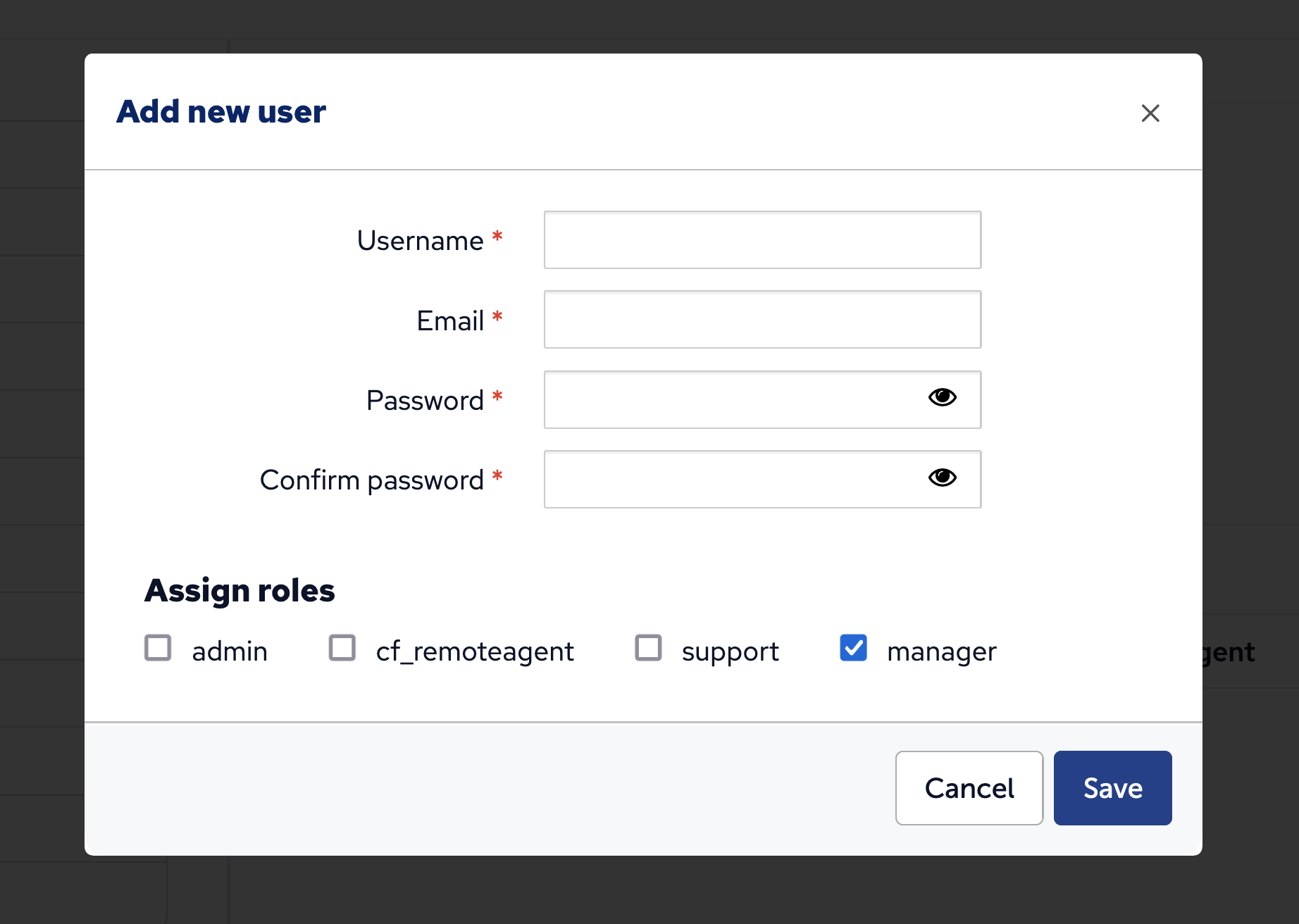
User management
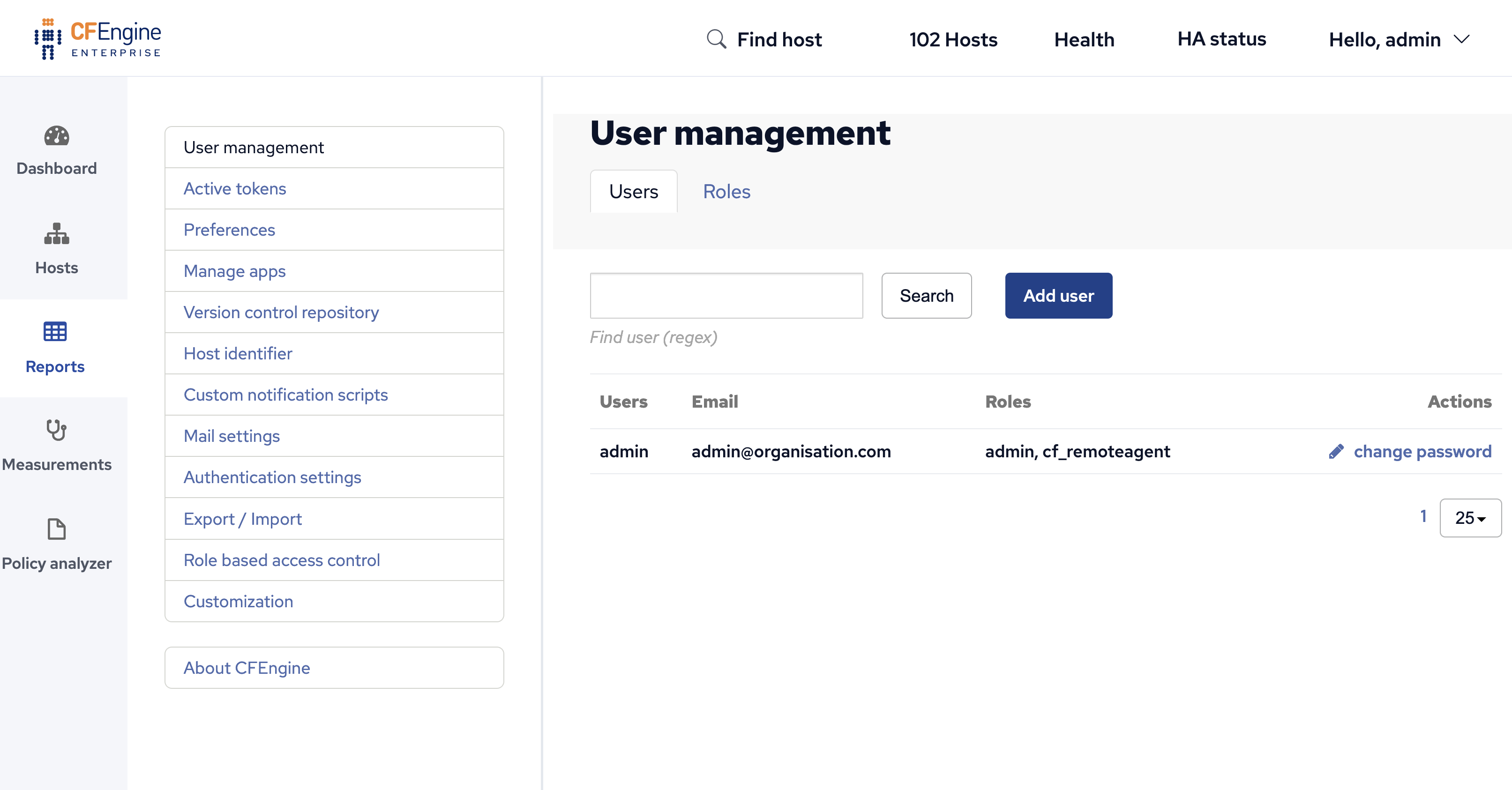
User management is for adding or adjusting CFEngine Enterprise UI users, including their name, role, and password.
Role management
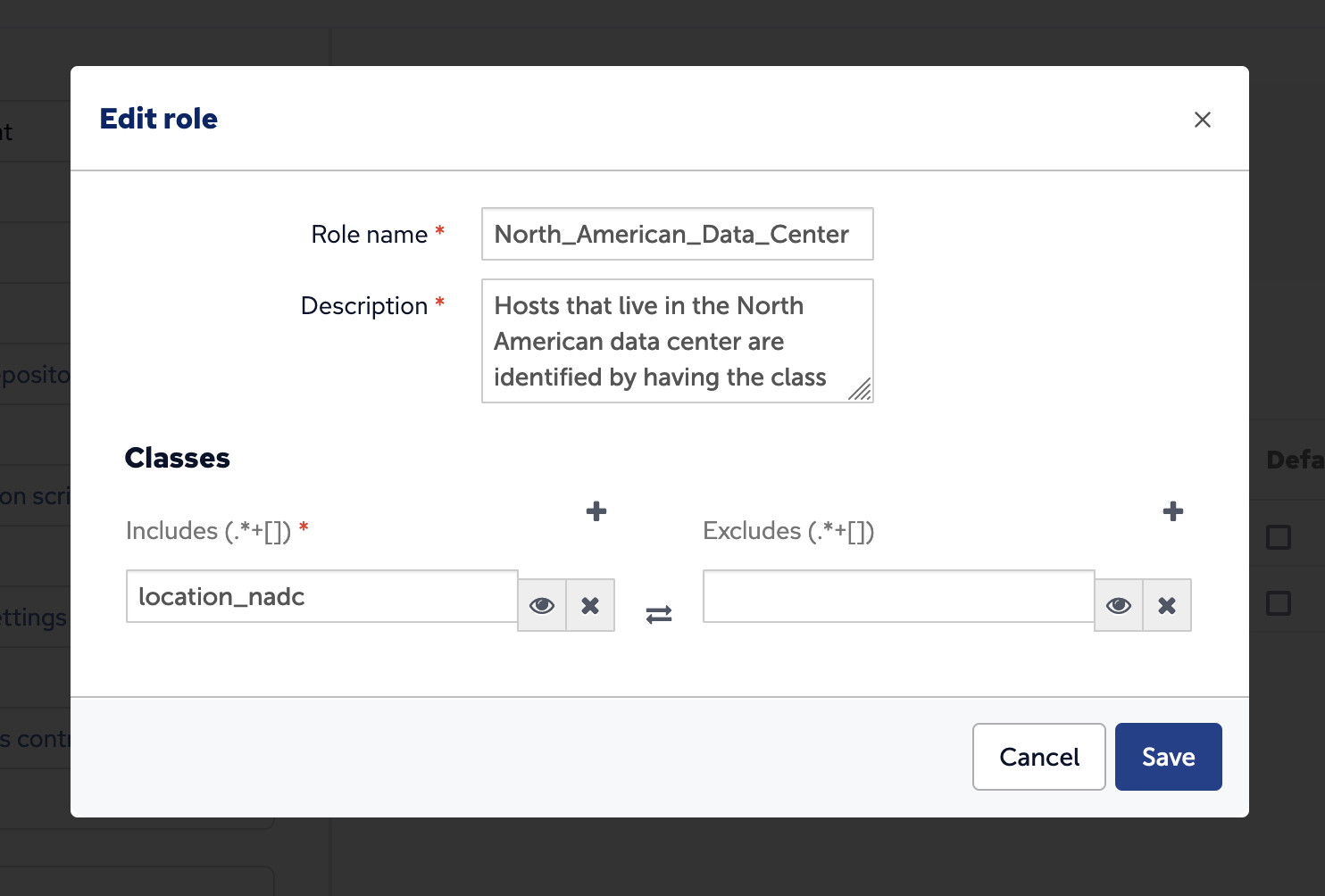
Roles limit access to host data and access to shared assets like saved reports and dashboards.
Roles limit access to which hosts can be seen based on the classes reported by
the host. For example if you want to limit a users ability to report only on
hosts in the "North American Data Center" you could setup a role that includes
only the location_nadc class.
When multiple roles are assigned to a user, the user can access only resources that match the most restrictive role across all of their roles. For example, if you have the admin role and a role that matches zero hosts, the user will not see any hosts in Mission Portal. A shared report will only be accessible to a user if the user has all roles that the report was restricted to.
In order to access a shared reports or dashboard the user must have all roles that the report or dashboard was shared with.
In order to see a host, none of the classes reported by the host can match the class exclusions from any role the user has.
Users without a role will not be able to see any hosts in Mission Portal.
Here is a set of example roles, users and the impact on each user will be able to view.
Example roles
Role suse:
- Class include: SUSE
- Class exclude: empty
Role cfengine_3:
- Class include: cfengine_3
- Class exclude: empty
Role no_windows
- Class include: cfengine_3
- Class exclude: windows
Role windows_ubuntu
- Class include: windows
- Class include: ubuntu
- Class exclude: empty
Example users
User one has role SUSE.
User two has roles no_windows and cfengine_3.
User three has roles windows_ubuntu and no_windows.
What reports each user can view
A report shared with SUSE and no_windows will not be seen by any of the listed users.
A report shared with no_windows and cfengine_3 will only be seen by user two.
A report shared with SUSE will be seen by user one.
Which hosts each user can view
User one will only be able to see hosts that report the SUSE class.
User two will be able to see all hosts that have not reported the windows class.
User three will only be able to see hosts that have reported the ubuntu class.
Predefined roles
admin- The admin role can see everything and do anything.cf_remoteagent- This role allows execution ofcf-runagent.
Default role
To set the default role, click Settings -> User management -> Roles. You can then select which role will be the default role for new users.
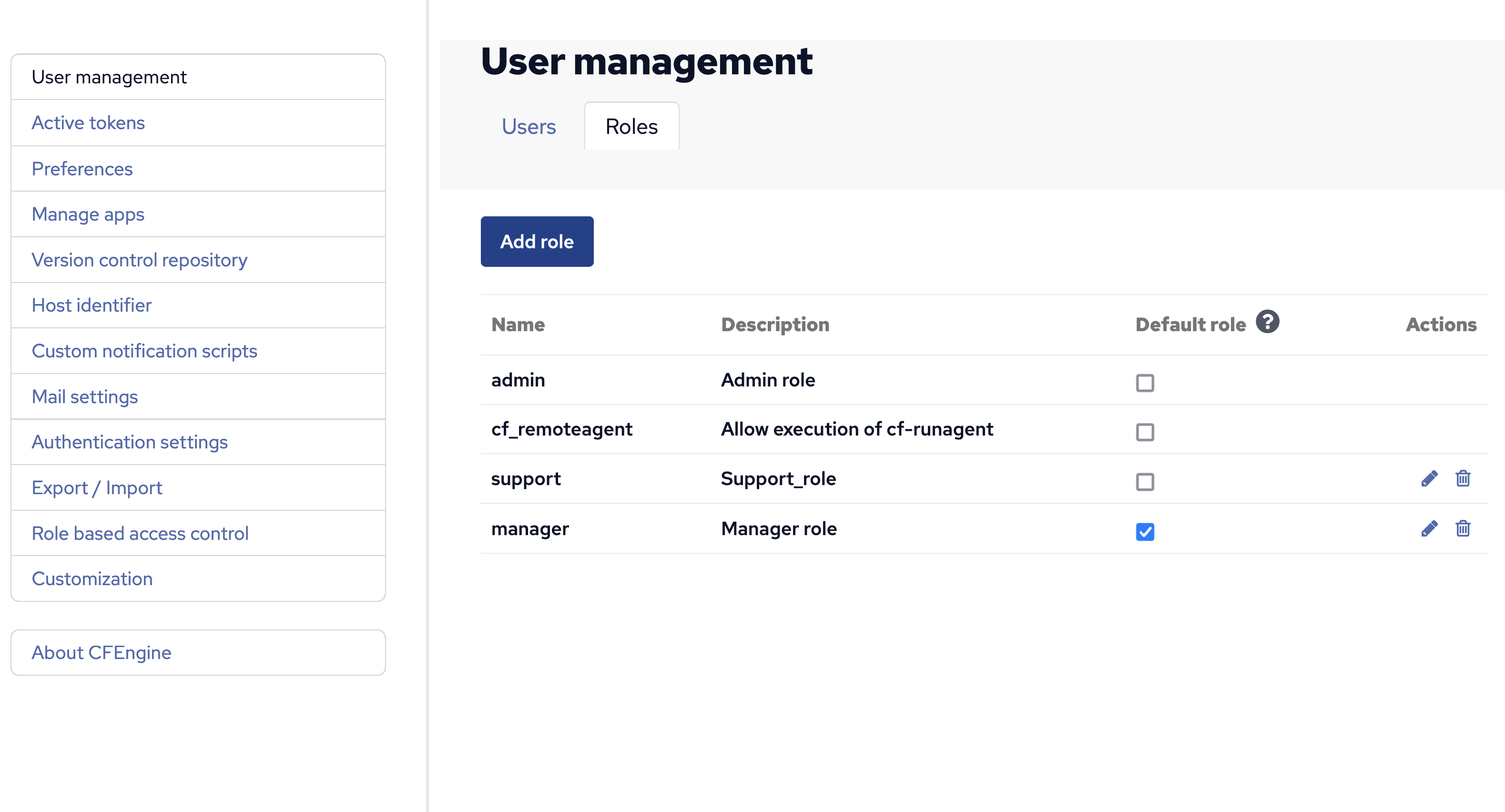
Behaviour of default role:
Any new users created in Mission Portal's local user database will have this new role assigned.
Users authenticating through LDAP (if you have LDAP configured in Mission Portal) will get this new role applied the first time they log in.
Note that the default role will not have any effect on users that already exist (in Mission Portal's local database) or have already logged in (when using LDAP).
In effect this allows you to set the default permissions for new users (e.g. which hosts a user is allowed to see) by configuring the access for the default role.
Manage apps
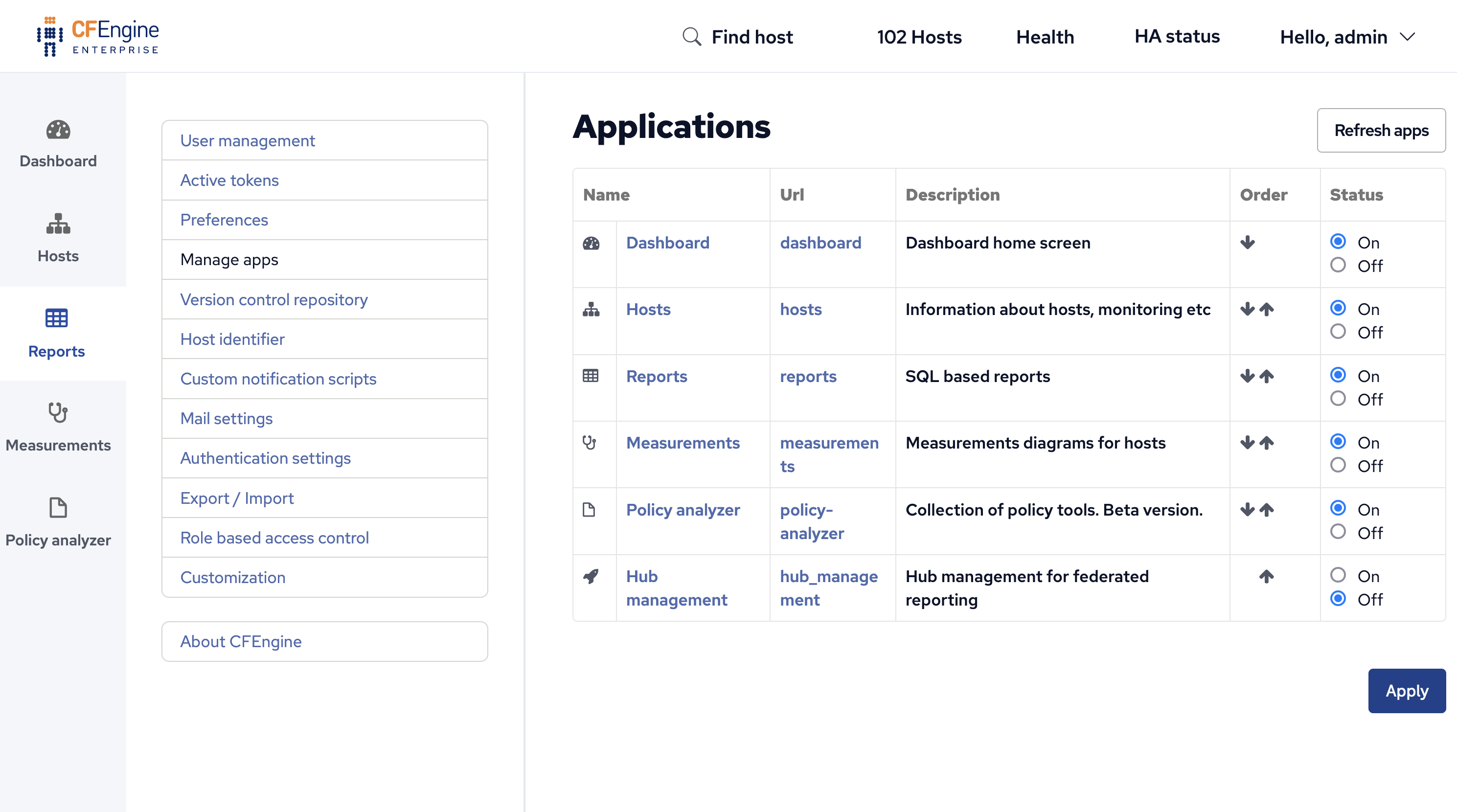
Application settings can help adjust some of CFEngine Enterprise UI app features, including the order in which the apps appear and their status (on or off).
Version control repository
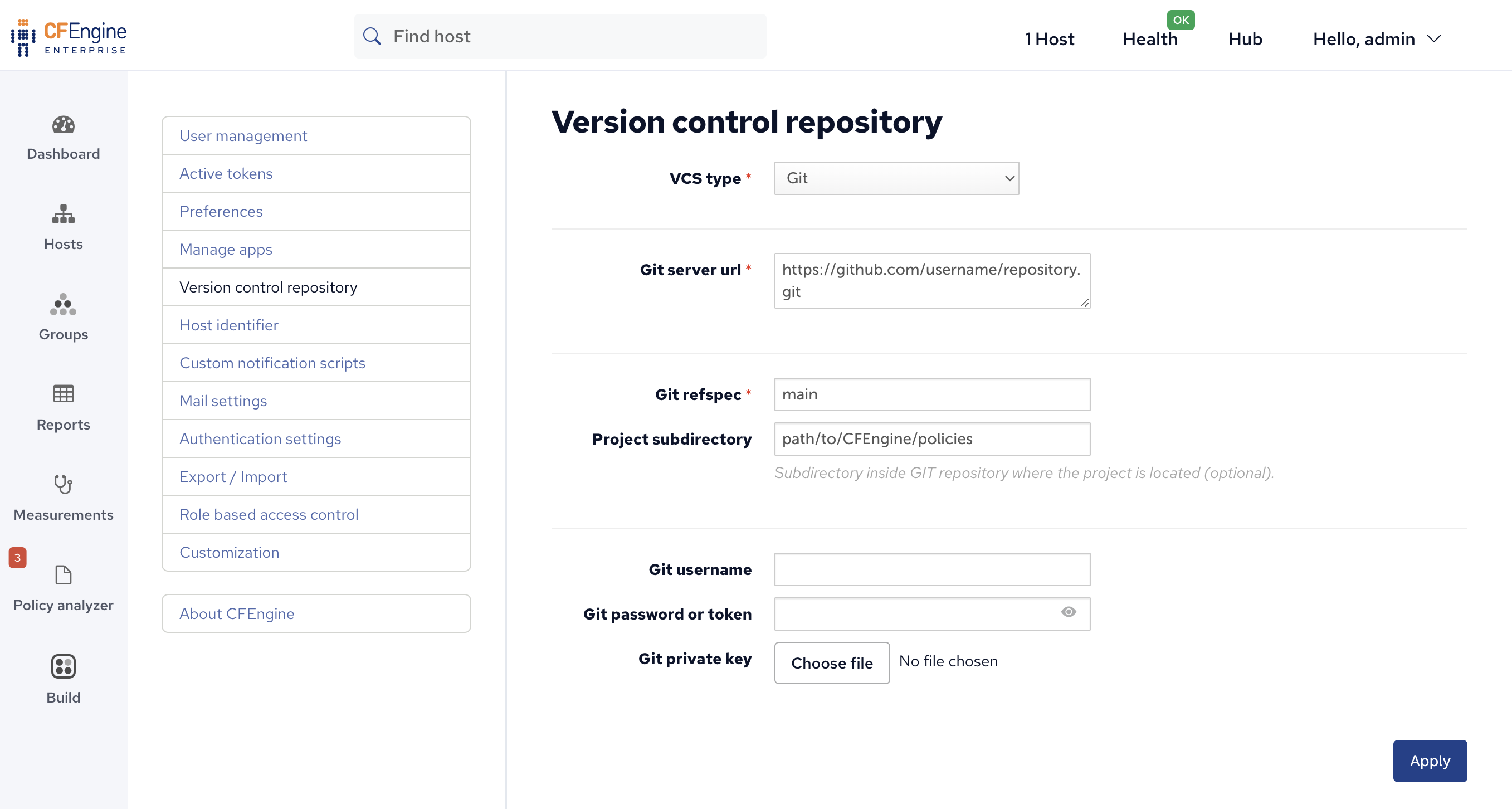
The repository holding the organization's masterfiles can be adjusted on the Version control repository screen.
Host identifier
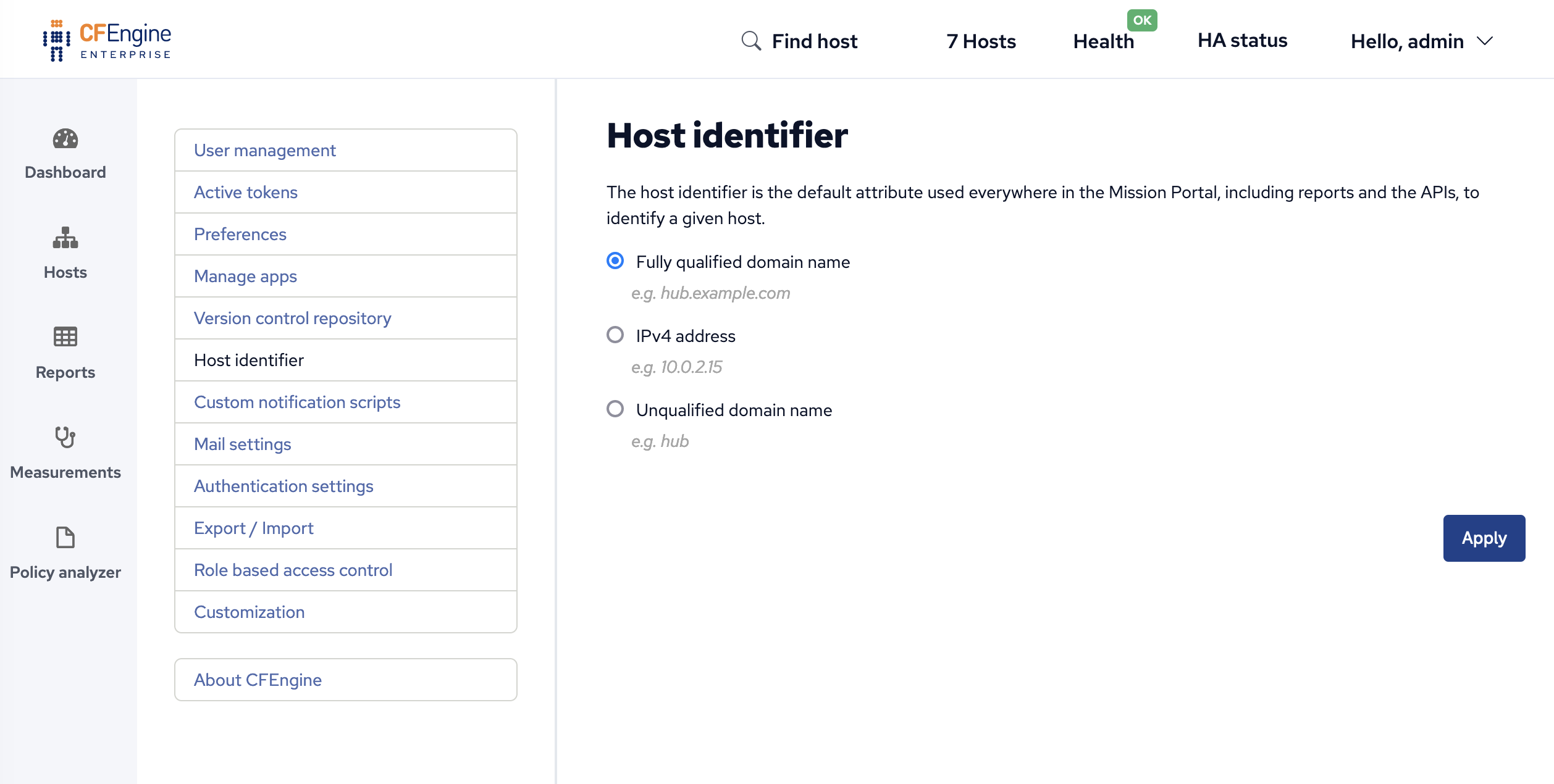
Host identity for the server can be set within settings, and can be adjusted to refer to the FQDN, IP address, or an unqualified domain name.
Mail settings
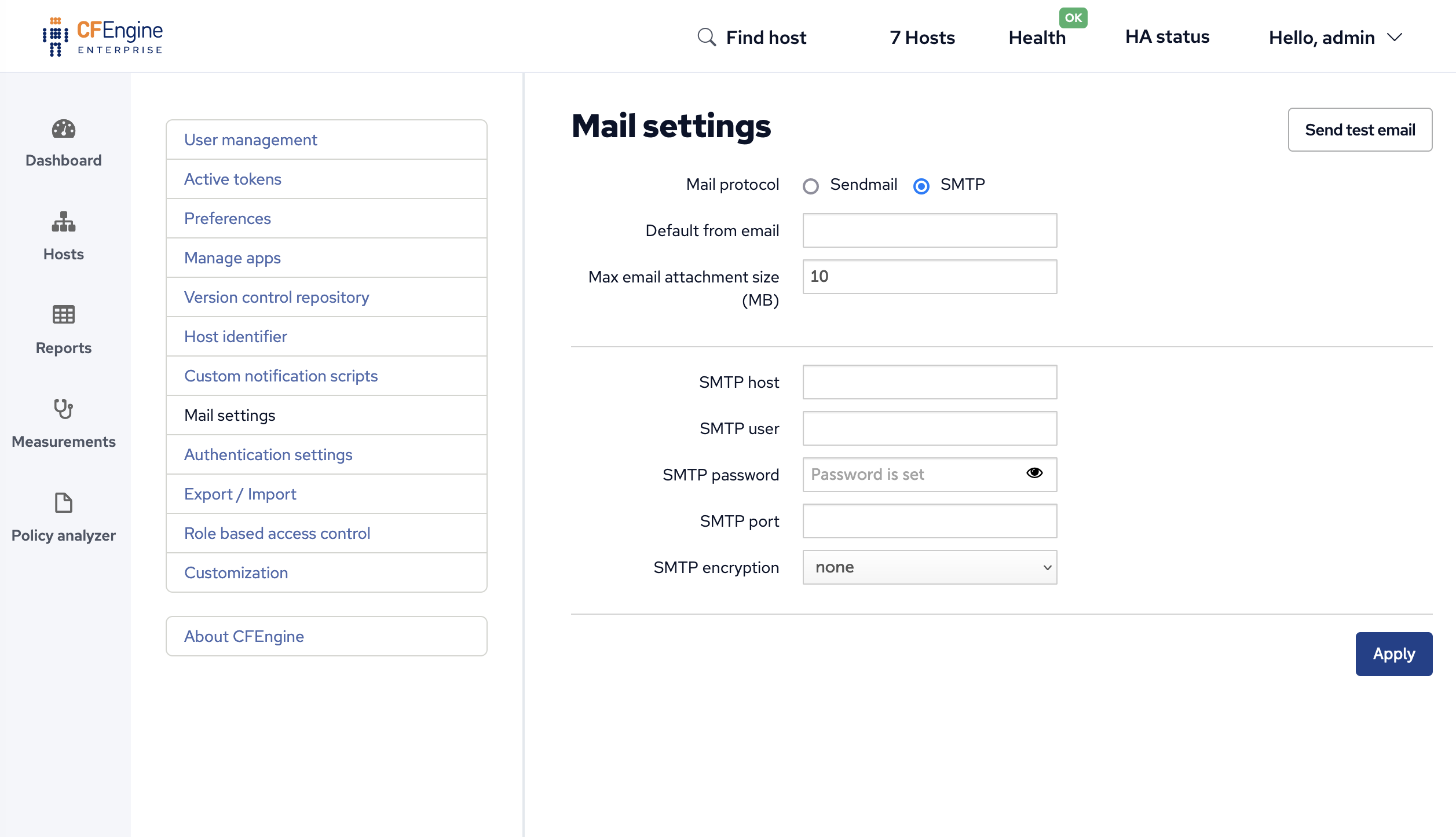
Configure outbound mail settings:
Default from email : Email address that Mission Portal will use by default when sending emails.
Mail protocol : Use the system mailer (Sendmail) or use an SMTP server.
Max email attachment size (MB) : mails sent by Mission Portal with attachments exceeding this will have the attachment replaced with links to download the large files.
Authentication settings
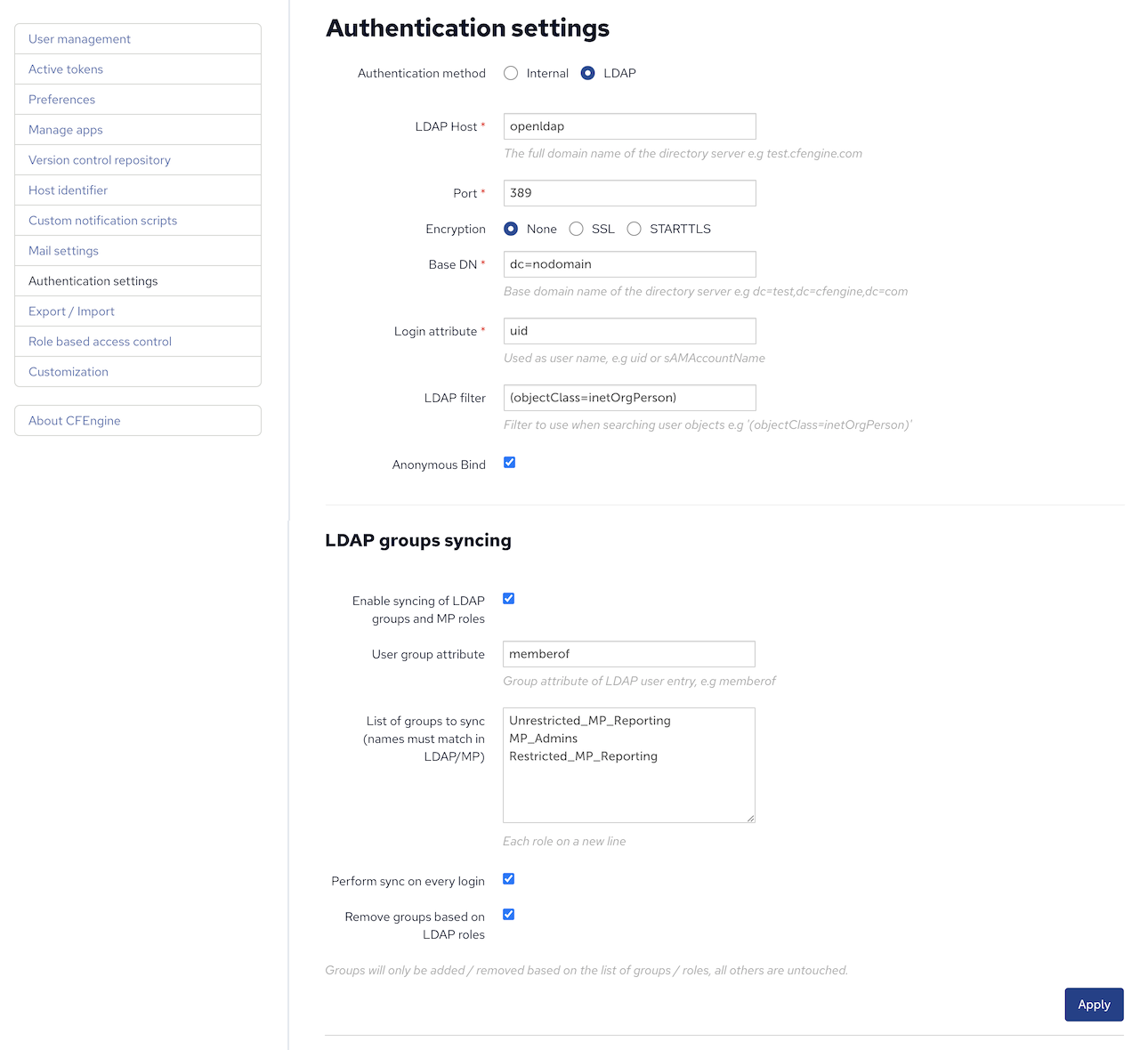
Mission portal can authenticate against an external directory.
Special notes:
- LDAP Host refers is the IP or Hostname of your LDAP server.
- LDAP filter must be supplied.
LDAP bind username should be the username used to bind and search the LDAP directory. It must be provided in distinguished name format. Additionally, you can bind anonymously.
Default roles for users is configured under Role management.
LDAP groups syncing
LDAP group syncing can be turned on by clicking the corresponding checkbox
- User group attribute must be provided to obtain groups from an LDAP user entity.
The default value for Active Directory is
memberOf. The group name will be taken fromcnattribute - List of groups to sync, names must match in LDAP/MP. Each role should be added on a new line.
- Click
Perform sync on every logincheckbox to synchronize user roles on every login, otherwise roles will be assigned to a user only on sign-up (first login).
- User group attribute must be provided to obtain groups from an LDAP user entity.
The default value for Active Directory is
Note: Roles must be created in Mission Portal. Enabling LDAP group sync will not result in addition or removal of Mission Portal roles.
See also: LDAP authentication REST API, Role management
Export/import
Mission Portal's configuration can be exported and imported.
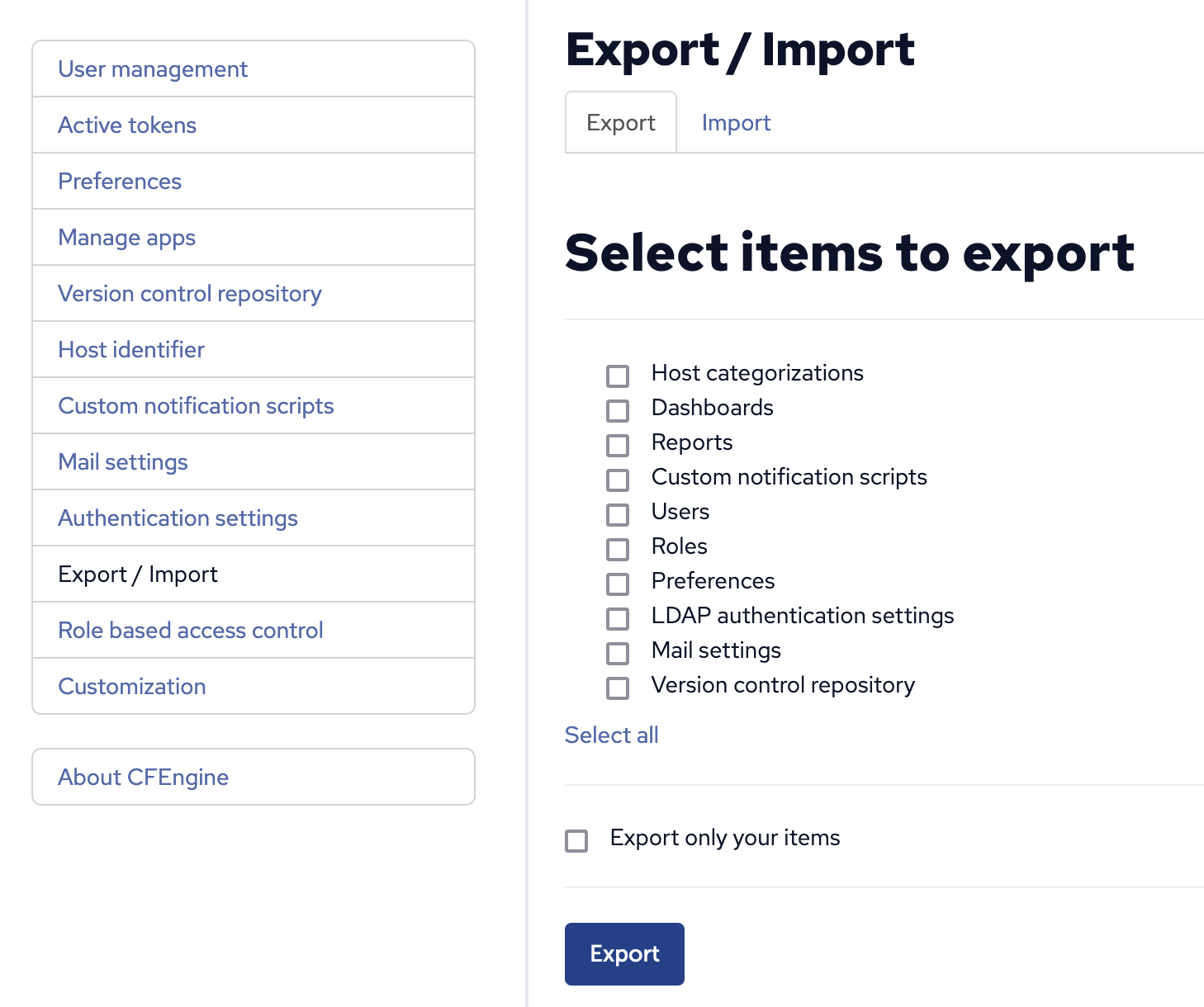
See also: Export/import API
Role based access control
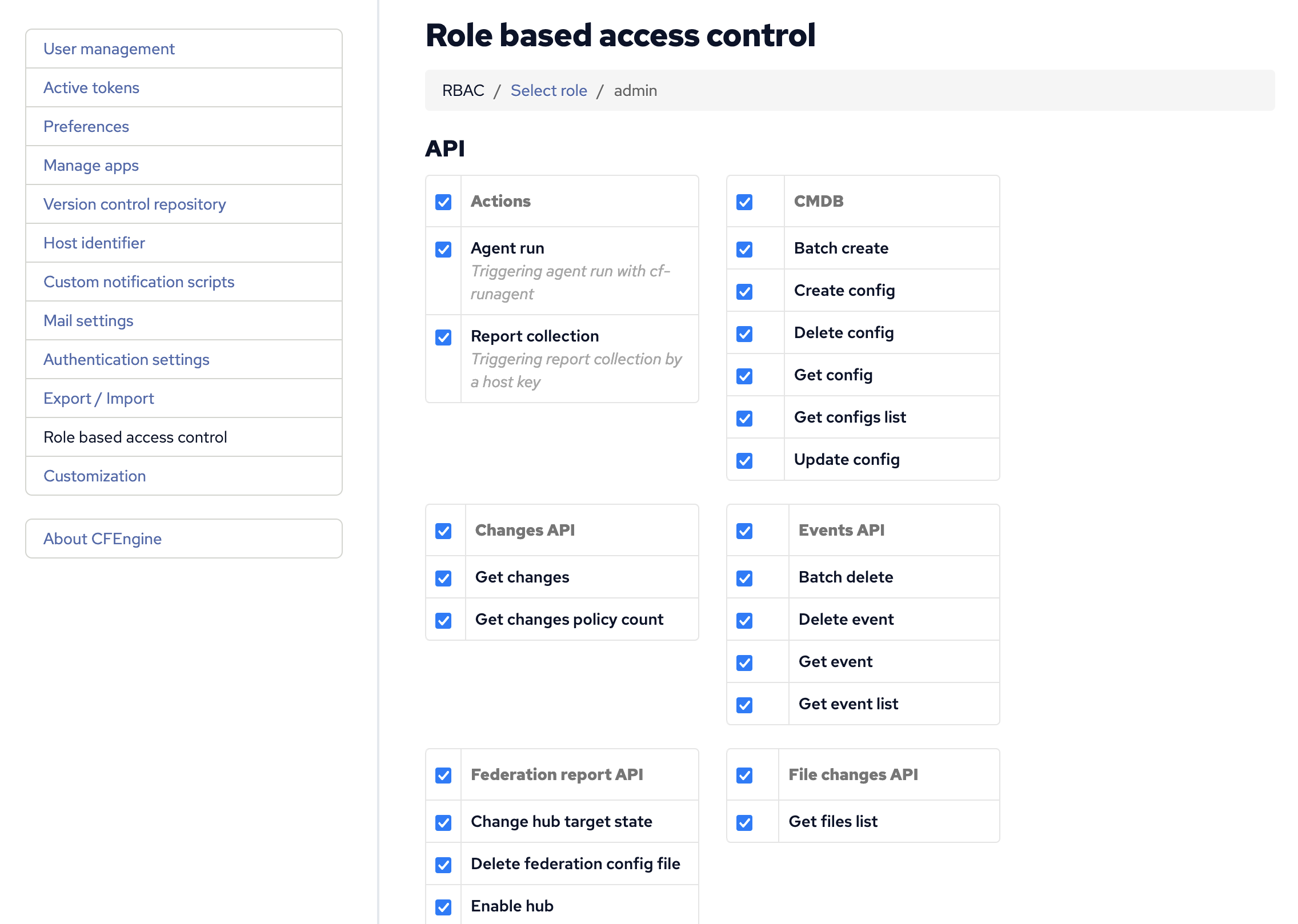
Roles in Mission portal can be restricted to perform only configured actions. Configure role-based access controls from settings.
Special notes:
Admin role has all permissions by default.
Cf_remoteagent role has all permissions related to API by default.
Permissions granted by roles are additive, users with multiple roles are permitted to perform actions granted by each role.
Restore admin role permissions:
To restore the CFEngine admin role permissions run the following sql as root on your hub
/var/cfengine/bin/psql cfsettings -c "INSERT INTO rbac_role_permission (role_id, permission_alias) (SELECT 'admin'::text as role_id, alias as permission_alias FROM rbac_permissions) ON CONFLICT (role_id, permission_alias) DO NOTHING;"
See also: Web RBAC API
About CFEngine
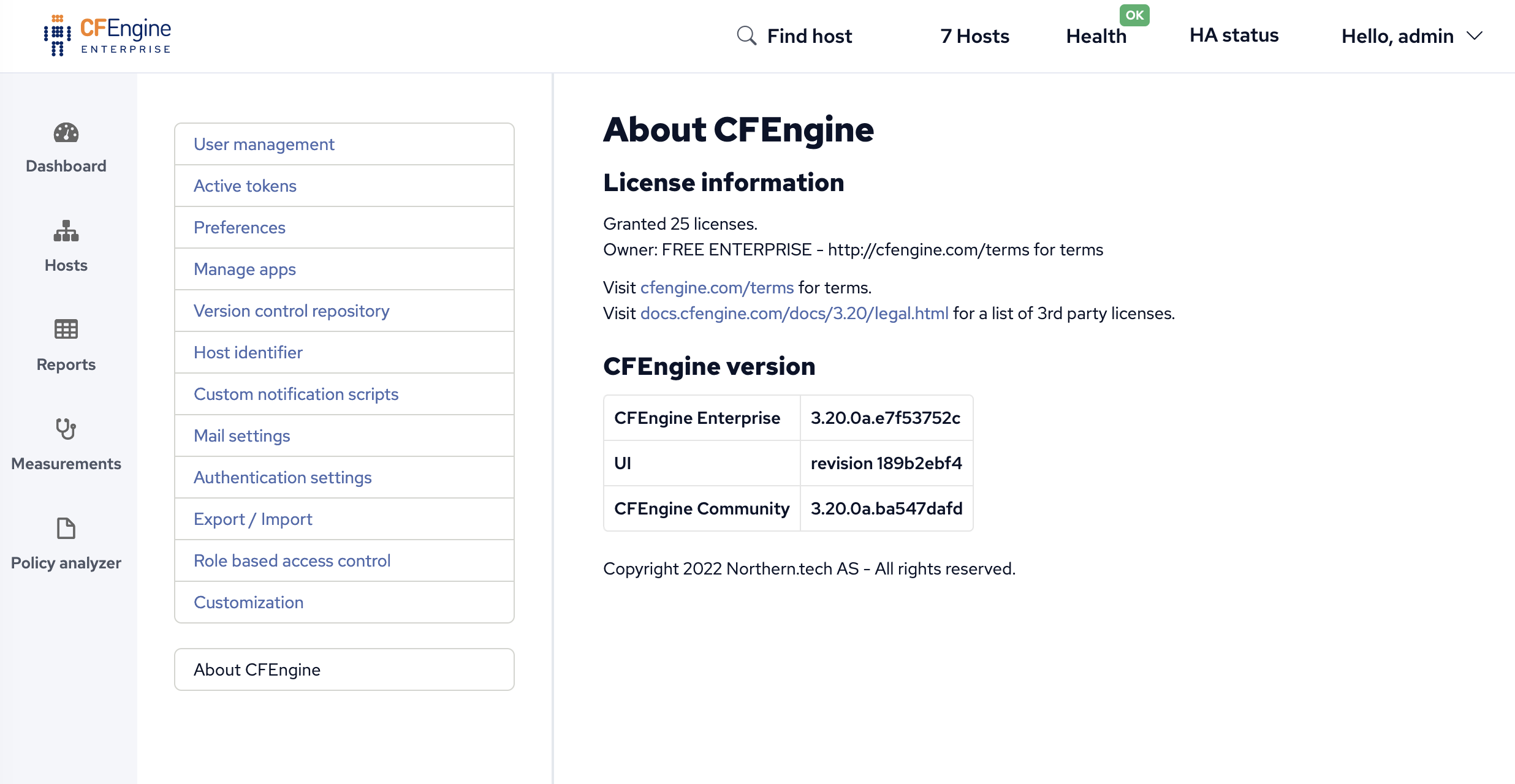
The About CFEngine screen contains important information about the specific version of CFEngine being used, license information, and more.

 Chat
Chat Ask a question on Github
Ask a question on Github Mailing list
Mailing list